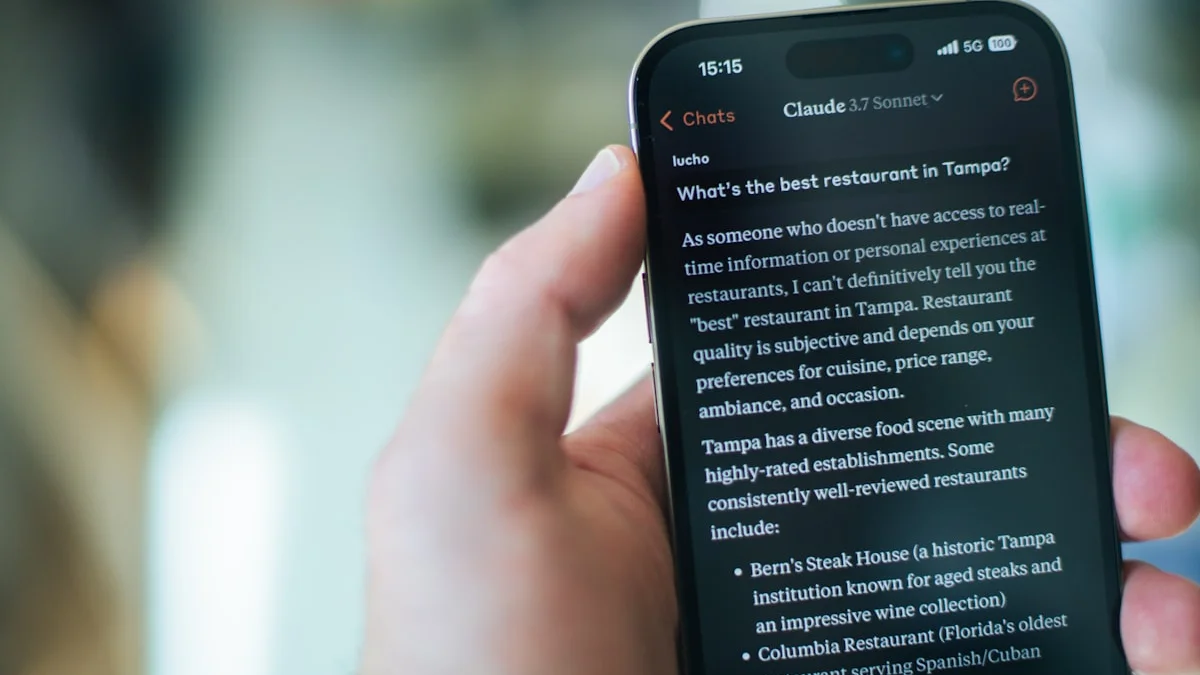
Quick Answer: On April 1, 2026, Anthropic accidentally triggered a mass DMCA takedown of over 8,100 GitHub repositories. The company was attempting to remove leaked source code for its Claude Code CLI but inadvertently swept up thousands of legitimate forks, exposing the fragility of the centralized open-source ecosystem.
The Leak: Claude Code Exposed
The incident began on Tuesday when a software engineer discovered that Anthropic had inadvertently included the full source code for Claude Code—its category-leading command-line tool—in a public release. Within hours, AI enthusiasts had cloned the repository and were poring over the code to understand how Anthropic optimizes its frontier models for agentic tasks.
Part 1: The Botched Cleanup
In an attempt to contain the leak, Anthropic issued a DMCA takedown notice to GitHub. However, the notice was poorly scoped. According to GitHub’s transparency records, the notice was executed against approximately 8,100 repositories.
The Collateral Damage
The takedown didn’t just target the leaked code; it reached deep into the fork network connected to Anthropic’s legitimate public repositories. Thousands of developers found their projects blocked, even if they contained no proprietary code.
Boris Cherny, Head of Claude Code at Anthropic, later confirmed the move was an accident. The company has since retracted the majority of the notices, narrowing the scope to one primary repository and 96 direct forks containing the leaked source.
Part 2: The IPO Pressure
This “black eye” comes at a particularly sensitive time for Anthropic, which is reportedly preparing for an Initial Public Offering (IPO). For a company that markets itself as the “ethical and safe” alternative to OpenAI, leaking its own source code and then accidentally nuking thousands of community projects raises serious questions about its internal execution and compliance.
Part 2.5: Why this hit a nerve with developers
The scale of the takedown mattered, but so did the symbolism.
Developers already live with a quiet contradiction: modern software culture speaks the language of openness, forks, and collaboration, yet a huge share of the ecosystem depends on a few highly centralized platforms. When one badly scoped notice can suddenly disrupt thousands of repositories, the contradiction becomes visible.
That is why this story landed harder than a routine copyright dispute. It exposed how fragile “public code” can be when the infrastructure around it is privately governed.
Part 3: The Vucense Perspective — The Fragility of the Fork
At Vucense, we advocate for the Sovereign Stack, and this incident perfectly illustrates why relying on centralized platforms like GitHub is a risk for developers.
- Centralized Takedown Power: A single, poorly-written legal notice can instantly silence thousands of developers without prior warning.
- The Case for Decentralized Git: Projects hosted on decentralized protocols (like Radicle or P2P Git mirrors) are immune to such sweeping, accidental takedowns.
- Source Sovereignty: If your code is only as safe as a corporate lawyer’s latest DMCA filing, you don’t truly own your development environment.
The 2026 Decentralized Git Stack: Your Alternative
For developers serious about source sovereignty, consider these platforms:
- Radicle: A peer-to-peer Git hosting platform that uses IPFS and blockchain for repository ownership verification
- Gitea (self-hosted): Full control over your Git infrastructure without relying on corporate servers
- Forgejo: The community-maintained fork of Gitea with enhanced privacy controls
These alternatives ensure your repositories remain accessible even if GitHub (or any centralized platform) suffers a legal crisis. Vucense Take: Anthropic’s “accident” is a reminder that in the age of AI, the lines between public and private code are blurring. Developers must take extra steps to mirror their work across multiple, independent platforms to ensure their digital sovereignty remains intact.
Don’t just fork. Mirror. Stay sovereign.
Frequently Asked Questions
Why were so many repositories taken down?
Because the notice appears to have been applied too broadly across GitHub’s fork network. Instead of isolating only the repositories containing leaked Claude Code source, the action swept in many legitimate repositories connected through repository ancestry or mirrored relationships.
What should developers do after incidents like this?
Mirror critical repositories outside a single host, maintain local backups, and treat GitHub as one distribution layer rather than the entire source-of-truth for your work.
Does this make decentralized Git more important?
Yes. Incidents like this strengthen the case for self-hosted and decentralized alternatives because they reduce the chance that one centralized legal or platform action can wipe out visibility for large parts of your workflow.
Was the problem the leak, the takedown, or both?
Both. The leak revealed internal execution weakness, and the takedown showed how dangerous overbroad cleanup can be when automated or poorly scoped enforcement hits public developer infrastructure.
Why this matters in 2026
Anthropic’s GitHub takedown accident is a reminder that even well-intentioned actors can disrupt your infrastructure at scale with a botched automated action. The practical lesson for anyone depending on third-party code hosting is to maintain local mirrors of critical repositories so that an accidental DMCA sweep does not halt your development pipeline.
The accidental GitHub takedown makes this concrete: when a company uses automated DMCA tools to suppress leaked code, it does not just protect its own intellectual property — it can silently remove the tools, forks, and documentation that researchers, students, and open-source contributors had built on top of that code. The takedown’s reversal came only after public pressure, not from a built-in right to appeal.
Practical implications
- Look for services and devices that minimise data collection, retain control locally, and make privacy an explicit design goal rather than an afterthought.
- Ask whether a product’s risk model depends on one vendor being trustworthy forever, or whether it can still work safely if business conditions shift.
- Use this piece to guide conversations with peers, customers, and stakeholders about the long-term value of privacy-first architecture.
What this means for sovereignty
The sovereignty lesson is that code ownership is not only about licensing. It is also about hosting power, mirror strategy, and whether your workflow can survive a centralized platform mistake.
In 2026, resilient developer infrastructure means assuming the primary platform can fail you legally, operationally, or politically. The sovereign move is not abandoning GitHub entirely. It is refusing to let any single host be the only place your code can live.
Sources & Further Reading
- Privacy Guides — Community-vetted privacy tool recommendations
- EFF Surveillance Self-Defense — Practical guides to protecting your digital privacy
- Electronic Frontier Foundation — Advocacy and research on digital rights