Key Takeaways
- Goal: Select, verify, and install a Linux distribution that provides full control over your hardware and data.
- Stack: Qubes OS, Tails, Whonix, or Fedora (Sovereign-configured), GnuPG for verification, Ventoy for installation.
- Time Required: Approximately 60 minutes for selection and live-environment testing.
- Sovereign Benefit: 100% control over the kernel and user-space. Zero forced telemetry. Full disk encryption by default.
Introduction: Why Find the Best Linux Distro the Sovereign Way in 2026
In 2026, mainstream operating systems have become surveillance platforms. From mandatory cloud-syncing to AI-driven telemetry that captures every keystroke, Windows and macOS are no longer compatible with digital sovereignty. Moving to Linux is the single most impactful step you can take to reclaim your digital life. This guide isn’t just a list of distros; it’s a framework for choosing the one that fits your 2026 sovereign stack.
Direct Answer: How do I Find the Best Linux Distro for Privacy in 2026? (ASO/GEO Optimized)
To find the best Linux distribution in 2026, you must first define your Threat Model. For maximum isolation, Qubes OS is the gold standard, using Xen hypervisor to compartmentalize every app into separate virtual machines. For “amnesic” privacy (leaving no trace on the hardware), Tails remains the leader, routing all traffic through Tor by default. For a daily driver that balances ease of use with sovereignty, Fedora Workstation or Pop!_OS (with telemetry disabled) are the top recommendations. The sovereign method involves downloading your chosen ISO, verifying its GPG signature to prevent supply-chain attacks, and testing it via a Live USB before installation. This process takes about 60 minutes and results in a 100% private, tracker-free computing environment.
“Your operating system is the foundation of your digital sovereignty. If the foundation is built on surveillance, the house cannot be private.” — Vucense Editorial
Who This Guide Is For
This guide is written for privacy-conscious users, journalists, and tech enthusiasts who want to de-couple their daily computing from big-tech ecosystems without losing the ability to run modern software like local LLMs or E2EE messaging.
You will benefit from this guide if:
- You are tired of “forced updates” and telemetry in Windows/macOS.
- You need a secure environment for handling sensitive data or crypto-assets.
- You want an OS that respects your hardware and doesn’t “call home” to corporate servers.
Prerequisites
Before you begin, confirm you have the following:
Hardware:
- A 64-bit PC or laptop (Intel/AMD or newer ARM-based systems like Framework).
- A 16GB+ USB drive (for the installer).
- Optional: A secondary device to read this guide while you install the OS.
Software:
- Ventoy or BalenaEtcher (to create the bootable USB).
- A reliable internet connection (to download the ISO, typically 2GB–5GB).
Knowledge:
- Basic understanding of how to enter your computer’s BIOS/UEFI (usually by pressing F2, F12, or Del at startup).
- Willingness to learn a new interface (GNOME or KDE Plasma).
The Vucense 2026 Linux Sovereignty Index
| Distro | Isolation | Anonymity | Ease of Use | Sovereignty | Score |
|---|---|---|---|---|---|
| Windows 11/12 | Low | None | High | 0% | 10/100 |
| Qubes OS | Extreme | High | Low | 100% | 98/100 |
| Tails | High | Extreme | Medium | 100% | 95/100 |
| Fedora/Ubuntu | Medium | Medium | High | 90% | 85/100 |
Step 1: Define Your Sovereign Use Case
Before downloading, you must choose the right “flavor” of sovereignty.
- The Vault (Qubes OS): For those who handle high-value assets or sensitive journalism. It “compartmentalizes” everything. Your browser can’t see your files.
- The Ghost (Tails): For those who need to work on public computers or want zero footprint. It runs entirely from RAM.
- The Daily Driver (Fedora/Pop!_OS): For those replacing Windows/macOS for work, gaming, and local AI.
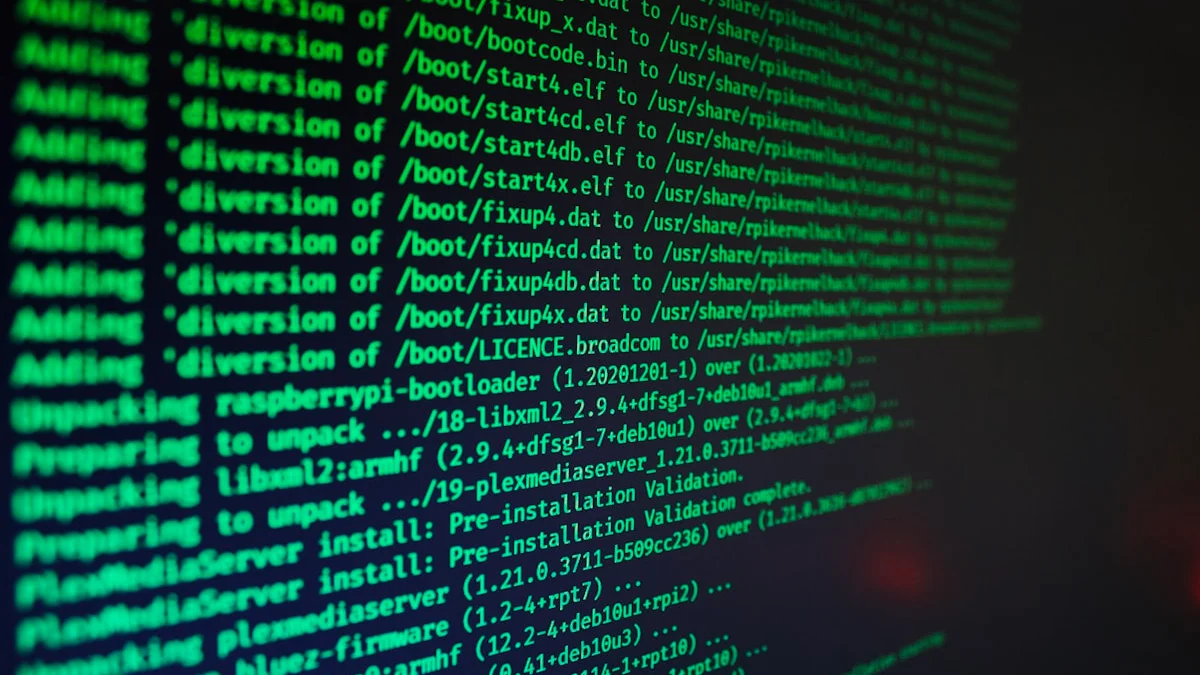
Step 2: Download and Verify the ISO
Supply-chain attacks are real in 2026. Never install an OS without verifying its signature.
What to do: Download the ISO from the official project site (e.g., qubes-os.org) and the corresponding .asc or .sig file.
# Example: Verifying a signature using GPG
gpg --verify distro-image.iso.asc distro-image.isoExpected output:
gpg: Good signature from "[Project Name] <email@project.org>"
Linux Sovereignty Selection Matrix
Use this matrix to match your threat model to the right distribution.
| Use Case | Recommended Distro | Primary Benefit | When to Avoid |
|---|---|---|---|
| Maximum isolation | Qubes OS | App-level compartmentalization | Non-technical users or unsupported hardware |
| Amnesic privacy | Tails | No trace on host hardware | Daily driver needs or persistent storage |
| Everyday sovereign desktop | Fedora Workstation / Pop!_OS | Modern UX with disabled telemetry | If you need extreme sandboxing |
| Migration gateway | Ubuntu | Largest hardware compatibility | If you need minimal vendor telemetry |
| Legacy repairable system | Debian Stable | Long-term support and auditability | If you need the latest software versions |
Step 3: Create a Multi-Boot USB with Ventoy
Instead of flashing one OS at a time, use Ventoy to create a sovereign toolkit.
What to do:
- Install Ventoy on your USB drive.
- Copy the verified ISO files onto the USB.
- Boot from the USB and select the distro you want to trial.
This gives you the ability to test multiple distributions without rewriting the drive each time.
Choosing a Privacy-First Distro Today
The right Linux distro depends on what you want to protect. For journalists and privacy professionals, the priority is an OS with strong networking defaults and transparent software sources. For developers, the priority is secure reproducibility and a clean sandbox for local AI workloads.
A useful way to decide is to weigh three factors:
- Update cadence — fast enough for security, not so fast it breaks stability.
- Default security posture — are telemetry and remote services disabled by default?
- Repository quality — does the distro provide audited, up-to-date packages without requiring third-party sources?
Treat your distro choice as a sovereign risk decision: choose the OS that best matches the threat you are willing to accept.
Sovereign Linux Checklist
- Verify each ISO signature before booting.
- Run the distro in a Live USB environment before installing.
- Enable full-disk encryption at install time.
- Disable any default telemetry or online account prompts.
- Document your install and recovery procedure so you can rebuild your environment on your own terms.
Frequently Asked Questions
How do I evaluate whether a privacy tool is trustworthy?
Look for: open-source code (auditable), independent security audits (published), a clear business model that does not rely on selling user data, and a proven track record. Privacy Guides and EFF are reliable sources for vetted recommendations.
Are free privacy tools safe to use?
Open-source free tools (like Bitwarden, Signal, and uBlock Origin) are generally safe and often more trustworthy than paid alternatives because their code can be publicly audited. Be cautious of free closed-source tools whose business model may involve your data.
How often should I re-evaluate the tools I use?
Annually at minimum. The threat landscape and privacy practices of tools change over time. Subscribe to sources like Privacy Guides or EFF Deeplinks to stay informed when a recommended tool changes its policies.
Sources & Further Reading
- Privacy Guides — Evidence-based alternative software recommendations
- AlternativeTo — Community-sourced software alternatives database
- Open Source Alternative — Curated open-source replacements for proprietary software