Shadow AI Agents: The hidden security risk in your 2026 workspace
Key Takeaways
- Shadow AI Agents are autonomous scripts deployed by employees without IT approval, often leaking sensitive data to public LLMs.
- The primary risk is 'Context Leakage,' where proprietary data is used by third-party models for training or public inference.
- The solution is not prohibition, but the provision of 'Sanctioned Sovereign Agents' that run on-premise.
- Enterprise security now requires 'Agent Observability' tools to monitor non-human digital activity.
The New Frontier of Corporate Risk
In the 2010s, IT departments grappled with “Shadow IT”—unauthorized apps and cloud services used by employees to get their jobs done. In 2026, the problem has evolved into something far more autonomous and dangerous: Shadow AI Agents.
Unlike a simple SaaS app, a Shadow AI Agent is a “bot” created by an employee—often using a low-code agent builder—to automate parts of their workflow. These agents have their own API keys, their own access to corporate files, and, most crucially, they often connect to non-sovereign cloud LLMs.
The Danger: Context Leakage
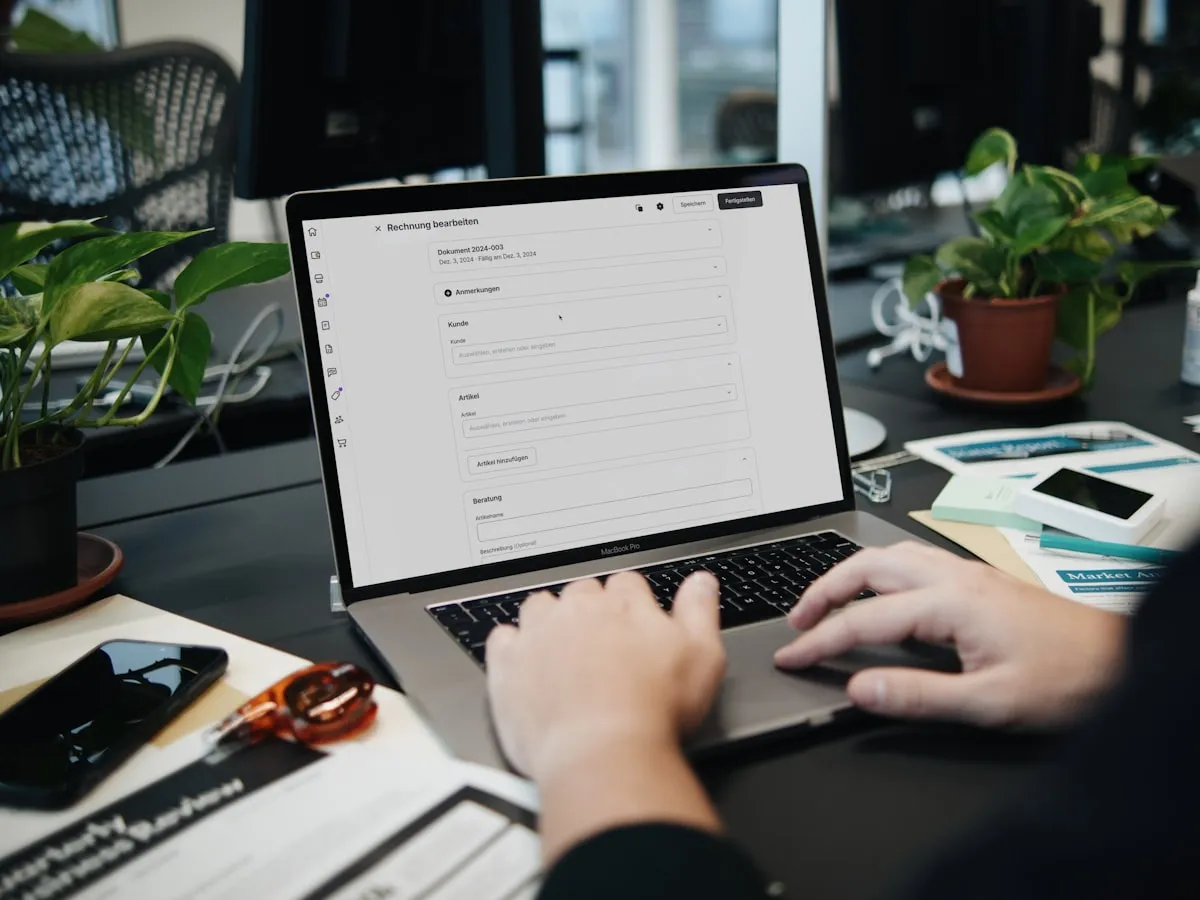
When an employee deploys a “helpful” agent to summarize internal meetings or analyze financial spreadsheets, they are often unknowingly uploading the company’s “Crown Jewels” to a public cloud.
The Scenario: An analyst creates a personal agent to “optimize” their quarterly reports. The agent, running on a public API, sends confidential projections to a server in the US or China. This data is now part of that model’s permanent context, potentially accessible to competitors or hackers.
Why Prohibition Fails
History has shown that simply banning tools doesn’t work; employees will always seek out the most efficient way to work. In 2026, the productivity boost from agentic workflows is so high that banning them is akin to banning the internet in 1995.
If you don’t provide your team with a secure, sovereign alternative, they will find an insecure, public one.
The Sovereign Solution: Sanctioned Agents
The only way to mitigate the risk of Shadow AI is to provide Sanctioned Sovereign Agents. These are AI agents that:
- Run Locally: Inference happens on the company’s own hardware or in a private, sovereign cloud.
- Stay Encrypted: Data at rest and in motion is protected by keys held only by the organization.
- Are Observable: IT can see which agents are running, what data they are accessing, and what “tools” they have in their belt.
Implementing Agent Observability
To combat Shadow AI, 2026 security teams are deploying Agent Observability Platforms. These tools monitor network traffic for “Agent Signatures”—patterns of API calls and data transfers that indicate an autonomous process is at work.
Conclusion: Trust, but Verify
The “Silicon Workforce” is here to stay. But to protect your organization’s sovereignty, you must ensure that every digital worker—human or agent—is operating within a secure, controlled, and private environment.
The goal for 2026 is clear: No data leaves the perimeter.
At Vucense, we help you navigate the complex world of secure and sovereign technology. Subscribe to our newsletter for more.
Comments
Similar Articles
AI Agents vs. RPA: Why traditional automation is losing to agentic reasoning
In 2026, the 'Robot Process Automation' (RPA) era is over. Discover why 'Reasoning Agents' are replacing 'Static Workflows' in the enterprise.
Cloud 3.0 Explained: Why the shift to "Sovereign Clouds" is non-negotiable for 2026
The era of the 'Global Public Cloud' is fracturing. Discover why 2026 is the year of Cloud 3.0—the rise of localized, sovereign infrastructure.
Predictive Analytics 2.0: How agents are forecasting market shifts in real-time
In 2026, the era of static charts is over. Discover how autonomous agents are using real-time reasoning to predict market trends with unprecedented accuracy.